ECIES with GoWith ECIES we use the public key from Elliptic Curve Cryptography in order to derive a symmetric key. In this case we create a symmetric key from Elliptic Curve Cryptography, and then use this to encrypt with AES-GCM: |
Theory
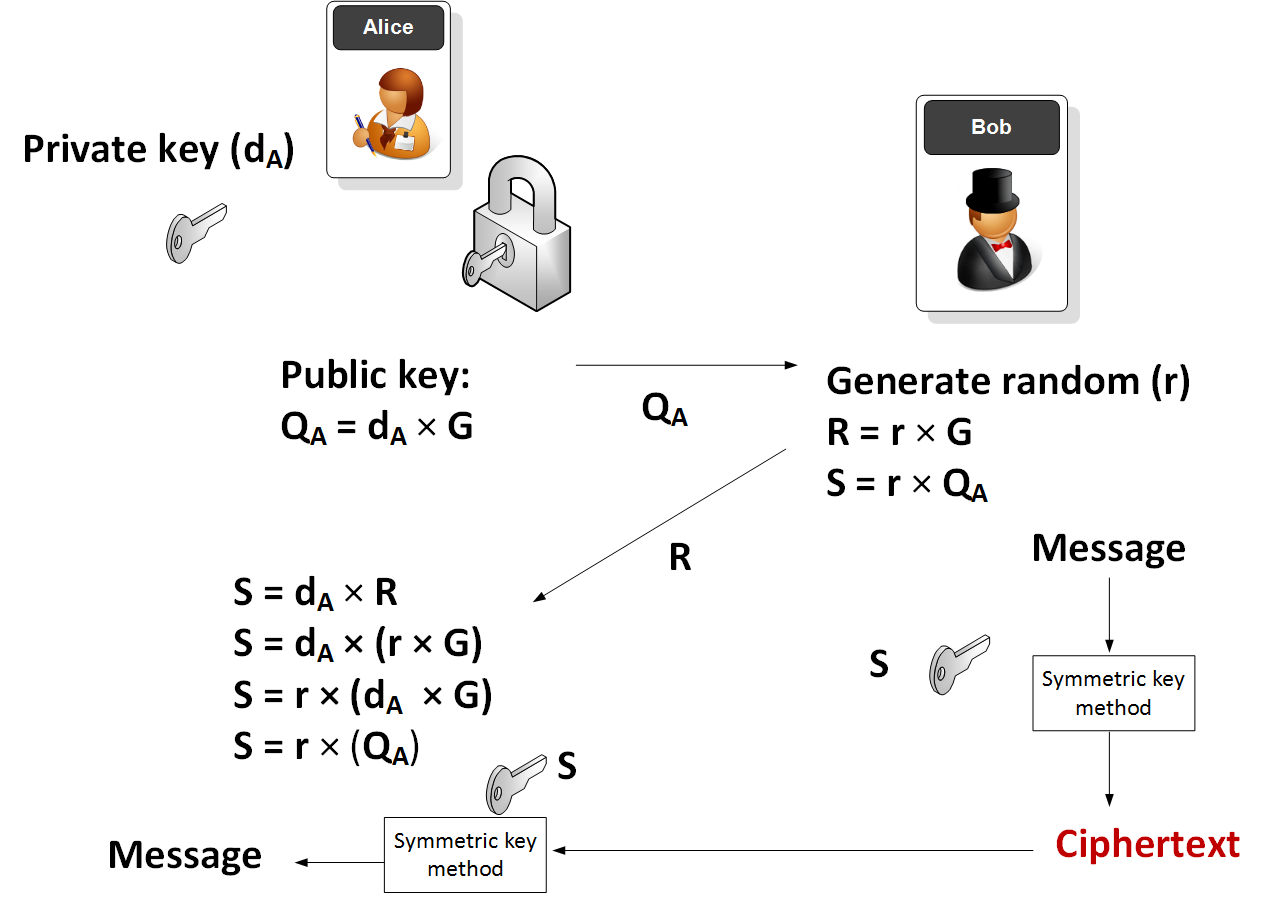
In this method Alice generates a random private key (\(d_A\)) and the takes a point on an elliptic curve (\(G\)) and then determines her public key (\(Q_A\)):
\(Q_A = d_A \times G\)
G and \(Q_A\) are thus points on an elliptic curve. Alice then sends \(Q_A\) to Bob. Next Bob will generate:
\(R = r \times G\)
\(S = r \times Q_A\)
and where r is a random number generated by Bob. The symmetric key (S) is then used to encrypt a message.
Alice will then receive the encrypted message along with \(R\). She is then able to determine the same encryption key with::
\(S = d_A \times R\)
which is:
\(S = d_A \times (r \times G)\)
\(S = r \times (d_A \times G)\)
\(S = r \times Q_A\)
and which is the same as the key that Bob generated.
The method is illustrated here:
Sample run
A sample run is:
Text input: Testing 123 Private key: 88378db4514d430d268a7a3e0f208b64bec637f3ffbaf7f1d012e6fcd815c809 Public key: a220e2df9623cde9a8f53fa80b87d2554ebc4c068285ffb009894d0399a56308 Cipher: 5fc6a08f93d3df3f178226185b797661add24a14c22a6ab4c2c792826ba159976a99ba33a1566169bef836d0452d1b444ca9461a3e989cbe9ece3b Decipher: Testing 123
Coding
The code is based on [here]:
package main
import (
"fmt"
"os"
"go.dedis.ch/kyber/v3/group/edwards25519"
"go.dedis.ch/kyber/v3/util/random"
"go.dedis.ch/kyber/v3/encrypt/ecies"
)
var rng = random.New()
func main() {
m:="Hello"
argCount := len(os.Args[1:])
if (argCount>0) {m= string(os.Args[1])}
message := []byte(m)
suite := edwards25519.NewBlakeSHA256Ed25519()
private := suite.Scalar().Pick(random.New())
public := suite.Point().Mul(private, nil)
ciphertext, _ := ecies.Encrypt(suite, public, message, suite.Hash)
fmt.Printf("Text input: %s\n\n",m)
fmt.Printf("Private key: %s\n",private)
fmt.Printf("Public key: %s\n\n",public)
fmt.Printf("Cipher: %x",ciphertext)
plaintext, _ := ecies.Decrypt(suite, private, ciphertext, suite.Hash)
fmt.Printf("\n\nDecipher: %s",plaintext)
}
For NIST P-256, we just add:
import (
"go.dedis.ch/kyber/group/nist"
)
suite := nist.NewBlakeSHA256P256()
For BN256 pairing, we just add:
import (
"go.dedis.ch/kyber/pairing"
)
suite := pairing.NewSuiteBn256()
 [
[