Chaffing and WinnowingChaffing and Winnowing is a method created by Prof Ron Rivest. |
Theory
Ron Rivest, in 1998, though proposed a method called Chaffing and Winnowing, and which uses keyless encryption. It involves separating out the useful parts of the transmitted message, and signing these parts with a valid MAC (Message Authentication Code), so that they parts can be authenticated. The sender then adds chaff and adds an incorrect MAC for these. At the other end, the receiver will know how to separate them, as the chaff will generate errors. If the codes are signed in some way, Eve cannot tell which is valid from the invalid.
With this method, Bob will authenticate each packet with a MAC, of which Alice has the secret key. He can also send bad packets with incorrect MACs, of which Alice will discard. For example, Bob sends:
(1. Hello [Good]) (1.Ankle [Bad]) (2.How [Good]) (2.Ill [Bad]) (3.Are [Good])(3.Also [Bod]) (4.You [Good])(4.Failure [Bad]])
so the message is actually "Hello How Are You"
For example we create a tuple for the data (serial, data, MAC). The message that Bob wants to send to Alice is:
{1, Please send me, 12345}
{2, Your details, 43546}
{3, As I am worried about you, 54354}
each of these messages have the correct MAC (12345, 43546 and 54354). Bob can then add some invalid ones:
{1, Please send me, 12345}
{1, Please go away, 8453}
{2, Your details, 43546}
{2, I don't want to see you, 53646}
{3, As I am worried about you, 54354}
{3, And that is the end of it, 44546}
In this case the new MAC codes are invalid (8453, 53646 and 44546), and thus Al-ice rejects them to give:
Please send me your details as I am worried about you
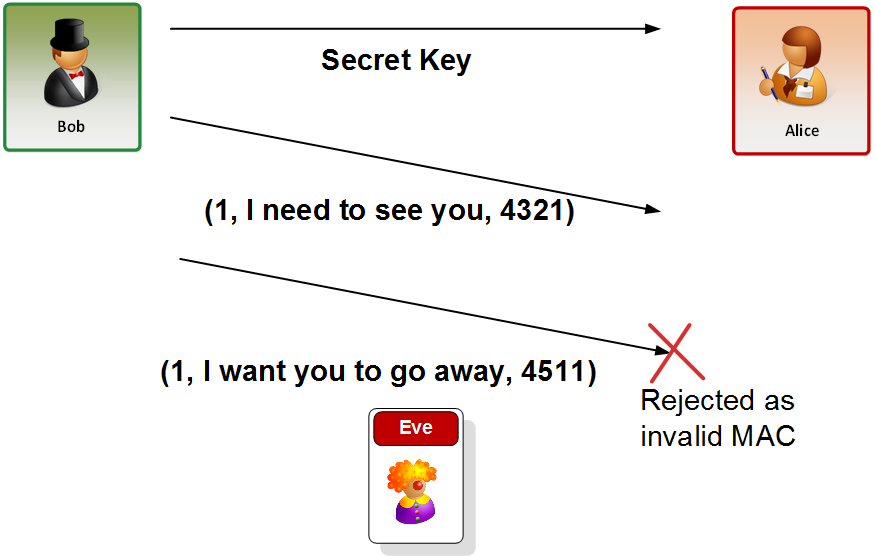
Figure 1 Adding chaff
With this we have a run of:
Original data [(1, 'bill', 'fred123'), (2, 'mike', 'password')] With chaff [(1, '\xa1\x8e?0', '0\xcb\x89~6\xdf\x9f'), (1, 'bill', 'fred123'), (2, 'mike', 'password'), (2, '\x06\x05\xefT', '\x81I\t\xdba\x82\x89L')] After chaff processed [(1, 'bill', 'fred123'), (2, 'mike', 'password')]