Authenticated ECDH with Curve X448 using Python
X448 is based on Curve 448, and is used for key exchange with ECDH (Elliptic Curve Diffie Hellman). It supports a 224-bit security level, and where we use a 448-bit (56-byte) prime number of \(P = 2^{448} - 2^{224} - 1\). It has improved security over Curve 25519, and which has a 255-bit prime number (\(P = 2^{255} - 19\)). As with X25519, in X448 we use a Montgomery curve (\(v^2 = u^3 + A \times u^2 + u\)) with scalar multiplication. In X448, we use 56-byte string values, rather than 32-byte values for X25519. Overall, X448 uses a little-endian method to store an array of bytes, and has a value of \(A = 39,081\). The base point \(G\) is at (5, 355293926785 ... 42774147268105838985595290606362), and the paramaters based by on RFC 7748 [here].
|
X2519 and ECDH
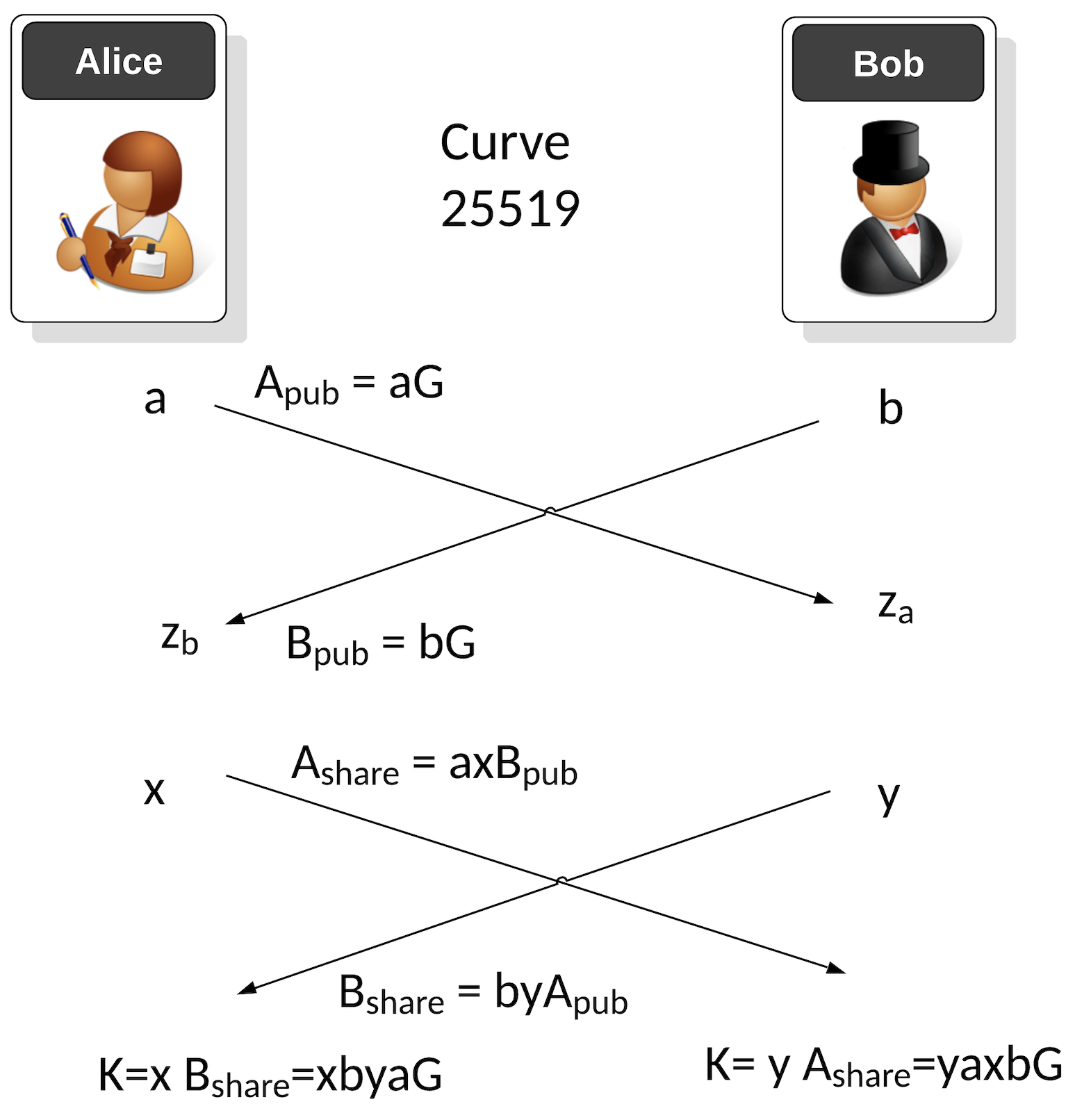
When Bob and Alice are communicating over a network, they might want to create a unique encryption key for each session. This is often achieved by using X448, and uses ECDH (Elliptic Curve Diffie Hellman). With this we select a base x co-ordinate point of G, and then Bob and Alice generate random values, and determine their public keys. Alice generates a long-term private key of \(a\), and Bob generates a long term private key of \(b\). Alice’s long public key will be:
\(A_{pub}= aG \pmod p\)
and Bob’s long-term public key becomes:
\(B_{pub}=bG \pmod p\)
Alice will store Bob's long-term key, and Bob will store Alice's long-term key, and they will use these to compute the shared key for each session. For a new session, Bob generates a random private key value of \(b\) and Alice generates a random private key of \(a\). Alice will then share a public key by and multiplying Bob's long term public key by \(a\) and \(x\):
\(A_{share}= a x B_{pub} = axbG \pmod p\)
And Bob takes Alice's public key and multiplies by \(b\) and \(y\):
\(B_{share}= b y A_{pub} = byaG \pmod p\)
The exchange their values, and Alice multiplies by the value received from Bob by \(y\), and Bob multiplies the value he receives from Alice by \(x\). They should then end up with the same value, and which should be:
\(A_{key}= yaxbG \pmod p = abxyG \pmod p\)
and:
\(B_{key}= xbyaG \pmod p = abxyG \pmod p\)
and which are the same values.
An overview is:
So here is a basic Python program to implement using X448:
import os
import binascii
from x448 import base_point_mult,multscalar
a = os.urandom(56)
b = os.urandom(56)
a_pub = base_point_mult(a)
b_pub = base_point_mult(b)
x = os.urandom(56)
y = os.urandom(56)
Bob_send = multscalar(y, a_pub) # (y) aG
Bob_send = multscalar(b, Bob_send) # (yb) aG
Alice_send = multscalar(x, b_pub) # (x) bG
Alice_send = multscalar(a, Alice_send) # (xa) bG
k_a = multscalar(x, Bob_send) # x (yb) aG
k_b = multscalar(y, Alice_send) # y ( xa) bG
print ("Bob private:\t",binascii.hexlify(a))
print ("Alice private:\t",binascii.hexlify(b))
print ("\n\nBob public:\t",binascii.hexlify(b_pub.encode()))
print ("Alice public:\t",binascii.hexlify(a_pub.encode()))
print ("\nBob x value:\t",binascii.hexlify(x))
print ("Alice y value:\t",binascii.hexlify(y))
print ("\n\nBob send:\t",binascii.hexlify(Bob_send.encode()))
print ("Alice send:\t",binascii.hexlify(Alice_send.encode()))
print ("\n\nBob shared:\t",binascii.hexlify(k_b.encode()))
print ("Alice shared:\t",binascii.hexlify(k_a.encode()))
# res=bytes_to_int(a)*bytes_to_int(y)*bytes_to_int(b)*bytes_to_int(x)
# k = base_point_mult(int_to_bytes(res,32))
# print ("\n\nChecking shared:\t",binascii.hexlify(k.encode()))
And here is x25519.py:
# X448
P = 2 ** 448 - 2 ** 224 - 1
A24 = 39081
def bytes_to_int(bytes):
result = 0
for b in bytes:
result = int(result * 256) + int(b)
return int(result)
def int_to_bytes(value, length):
result = []
for i in range(0, length):
result.append(value >> (i * 8) & 0xff)
return result
# Defined here https://tools.ietf.org/html/rfc7748
def cswap(swap, x_2, x_3):
dummy = swap * ((x_2 - x_3) % P)
x_2 = x_2 - dummy
x_2 %= P
x_3 = x_3 + dummy
x_3 %= P
return (x_2, x_3)
# Defined here https://tools.ietf.org/html/rfc7748
def X448(k, u):
x_1 = u
x_2 = 1
z_2 = 0
x_3 = u
z_3 = 1
swap = 0
for t in reversed(range(448)):
k_t = (k >> t) & 1
swap ^= k_t
x_2, x_3 = cswap(swap, x_2, x_3)
z_2, z_3 = cswap(swap, z_2, z_3)
swap = k_t
A = x_2 + z_2
A %= P
AA = A * A
AA %= P
B = x_2 - z_2
B %= P
BB = B * B
BB %= P
E = AA - BB
E %= P
C = x_3 + z_3
C %= P
D = x_3 - z_3
D %= P
DA = D * A
DA %= P
CB = C * B
CB %= P
x_3 = ((DA + CB) % P)**2
x_3 %= P
z_3 = x_1 * (((DA - CB) % P)**2) % P
z_3 %= P
x_2 = AA * BB
x_2 %= P
z_2 = E * ((AA + (A24 * E) % P) % P)
z_2 %= P
x_2, x_3 = cswap(swap, x_2, x_3)
z_2, z_3 = cswap(swap, z_2, z_3)
return (x_2 * pow(z_2, P - 2, P)) % P
def decodeScalar448(k):
k_list = [(b) for b in k]
k_list[0] &= 252
k_list[55] |= 128
return decodeLittleEndian(k_list)
def decodeLittleEndian(b):
return sum([b[i] << 8*i for i in range( 56 )])
def unpack2(s):
if len(s) != 56:
raise ValueError('Invalid Curve448 scalar (len=%d)' % len(s))
return sum(ord(s[i]) << (8 * i) for i in range(56))
def pack(n):
return ''.join([chr((n >> (8 * i)) & 255) for i in range(56)])
def clamp(n):
n &= ~3
n |= 128 << 8 * 55
return n
# Return nP
def multscalar(n, p):
n = clamp(decodeScalar448(n))
p = unpack2(p)
return pack(X448(n, p))
# Start at x=9. Find point n times x-point
def base_point_mult(n):
n = clamp(decodeScalar448(n))
return pack(X448(n, 5))
A sample run is:
Bob private: b'2b55865459c75edf393cd021f44e076d1c27ae633c84120e08b3155124f9f8149e3a95d10828d5dcab459e1e0559d0f646869e95a5768b58' Alice private: b'8a2925f54baacba7a635fa44d88acc4c99ee16596632063d3eac0a8cd6efd157e665d7cef5dc9d9e360531456e1d691b3c6e71ce423f293d' Bob public: b'33c3b7c2b83448c39c25626f7ac2bc3c6618c291c39fc38c60c290c3b2c2b3c382c3b5c3a24dc3bec28d6cc2a11f0827c38d673bc3b943c3a56c28c2b34b09c39ac3afc3bd27c2bac3aa29c3bdc2a4c3bcc3a60c20' Alice public: b'0719c39b6bc2a7c3bfc3b1c2835c5ac2aec3aac2a134c3b14417c3b80fc3a100764d3303c2bec29e2ec2821c09481747c38bc2afc3b8c2a26905c3bac3b4c2a1213ac3a9c381c286c2a8c299c291c298c3bb5ec29cc280' Bob x value: b'2e2d1fc41350aa6feba22c4fc5c7bb8b7e29fd1021e4555ffd3bd6f2ce4e6e177160630f6f3643c6e2ede1b26b77f46832af657e8419e0c4' Alice y value: b'32ba4d851deda407e2df3a486f443cbe9c8e4540d849f0a912b6edd574c031d98d4cebe0b46d104a92fedd157ab4b113d2527521067d0525' Bob send: b'3600c3a6c3a24150395a5c6e6669c384c38a05c3aec38a034523c3b34737c38ac3b9c382c2bbc381c2a10a3e1b5ac298260c29c3a3c3a7773a3900c2bec391c2bc73147f4fc2b45755c3b34c50' Alice send: b'233a0e31c38ac3b54ac2925170207b5912713dc3ae54c3a3c281572a2bc2a9c390c38e7ec38fc2b755c3acc2af52c394c2b8c3bc75c3ac5e54051345c3bac2a243c383c3a14505c384c2bdc293c3b377c2af' Bob shared: b'2fc28303c382c3b3c29b02c38b6e0076591fc39ac287c3b5c3ba38c2acc3b06e20c38534215543c3b16bc39a78666b480bc280c3b20510522cc38dc2b6c3a1c28901006c1cc2845b52c3943ec28cc391' Alice shared: b'2fc28303c382c3b3c29b02c38b6e0076591fc39ac287c3b5c3ba38c2acc3b06e20c38534215543c3b16bc39a78666b480bc280c3b20510522cc38dc2b6c3a1c28901006c1cc2845b52c3943ec28cc391'