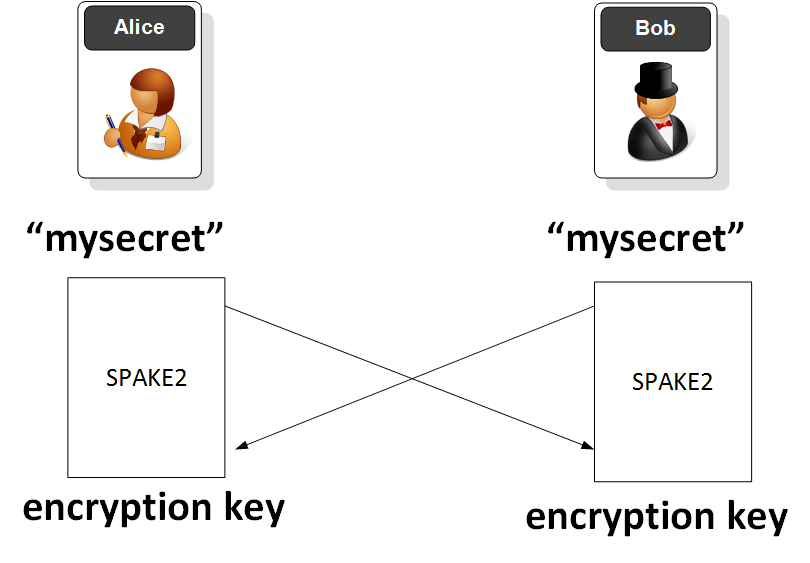
SPAKE2PAKE (password-authenticated key exchange) is one protocol which supports the hiding of a password from the network communications. With this we can have a relatively weak shared password on either side, and then communicate to determine a strong shared key. MethodIncreasingly we use ZKP (Zero-Knowledge Proofs) to prove that the Bob still has knowledge of his password. Another method is PAKE (password-authenticated key exchange) and which supports the hiding of a shared password within network communications. With this we can have a relatively weak shared password on either side, and then communicate to determine a strong shared key:
With SPAKE2 (derived from "password-authenticated key exchange"), Bob and Alice can derive a strong secret key based on a password that they both know. Eve, who is listening, will not be able to generate the same secret, even though she listens to their communications. If she tries to spoof Bob or Alice, she will only get one change to guess the password before she is locked-out. Thus, Bob and Alice can use a weak password, as Eve only gets one chance to guess. There is also no offline analysis, as the hand-shake must occur on-line. Along with this, there are no derived keys from previous sessions. Elliptic curve methods (using Curve 25519) are used to provide security methods that are equivalent to 128-bit AES. Often PAKE is used to do a one-time registration, and then generate a new key which becomes the long-term key. As with SRP, we can use PAKE as a log-in method, but its usage must be carefully analysed for risks. For SPAKE2, we have two roles: A (Alice) and B (Bob). They use two classes (SPAKE2_A and SPAKE2_B), and then pass messages to each other using these. Each time, Bob and Alice will generate a new key. Alice take the shared password and converts it into an integer (w). She then picks a random number (x) from 0 to p (a prime number), and which is divisible by h. She then calculates: \(X=xG\) and \(T=wM+X\) The value of \(T\) is sent to Bob. Bob also creates \(w\), and picks a random number (\(y\)) from 0 to \(p\) (a prime number). He then calculates: \(Y=yG\) and \(S=wN+Y\) Bob sends the value of Y to Alice. Alice calculates \(K(Alice)=x(S-wN)\), and Bob calculates \(K(Bob)=y(T-wM)\). These values are basically: \(K(Bob)= x (S-wN) = x (wN+Y-wN)=xY = xyG\) \(K(Alice)= y(T-wM) = y(wM+X-wN)=yX = xyG\) The values of \(N\) and \(M\) for elliptic curve are: M = d048032c6ea0b6d697ddc2e86bda85a33adac920f1bf18e1b0c6d166a5cecdaf seed: edwards25519 point generation seed (M) N = d3bfb518f44f3430f29d0c92af503865a1ed3281dc69b35dd868ba85f886c4ab seed: edwards25519 point generation seed (N) For the elliptic curve, G is a group of order \(p \times h\), where \(p\) a large prime number and \(h\) is the co-factor. All of the operations are conducted \(\pmod p\). The sample Python coding is: from spake2 import SPAKE2_A from spake2 import SPAKE2_B from spake2.parameters.i1024 import Params1024 from spake2.parameters.i2048 import Params2048 from spake2.parameters.i3072 import Params3072 import base64 import sys password="qwerty" par = "" print "Password for Bob and Alice is:",password if (par<>""): print "Security level:",par if (par=="Params1024"): par=Params1024 if (par=="Params2048"): par=Params1024 if (par=="Params3072"): par=Params3072 if (par==""): alice = SPAKE2_A(password) bob = SPAKE2_B(password) else: alice = SPAKE2_A(password,params=par) bob = SPAKE2_B(password,params=par) alice_out = alice.start() bob_out = bob.start() print "\nAlice passes:\t",base64.b64encode(alice_out) print "Bob passes:\t",base64.b64encode(bob_out) key1 = alice.finish(bob_out) key2 = bob.finish(alice_out) print "\nKey (Alice):\t",base64.b64encode(key1) print "Key (Bob):\t",base64.b64encode(key2) A sample run is: Password for Bob and Alice is: hello123 Alice passes: QRXpsrdkAC0xibdqTRLCOOLbvsO7jgvwsju6t9ZF/rsg Bob passes: QpVNlqLPQXAvWZSHgxOce86Vzryq1mH+8w6cs9ty8yzj Key (Alice): 7gbyqgfa5q+R513od++myShq/tC9C7NP+FEf34s8xP4= Key (Bob): 7gbyqgfa5q+R513od++myShq/tC9C7NP+FEf34s8xP4= The default is elliptic curve security, but we can use three integer-group parameter sets of Params1024, Params2048 and Params3072 and which gives 80-bit, 112-bit, and 128-bit security levels, respectively. PresentationThe following is an outline presentation on PAKE [slides]: |