SHA-3, Keccak and SHAKE are new hash functions [article].
SHA-3, Keccak and SHAKE |
Test vectors
The following are test vectors for "abc" [Test vectors]
SHA-3-224 e642824c3f8cf24a d09234ee7d3c766f c9a3a5168d0c94ad 73b46fdf SHA-3-256 3a985da74fe225b2 045c172d6bd390bd 855f086e3e9d525b 46bfe24511431532 SHA-3-384 ec01498288516fc9 26459f58e2c6ad8d f9b473cb0fc08c25 96da7cf0e49be4b2 98d88cea927ac7f5 39f1edf228376d25 SHA-3-512 b751850b1a57168a 5693cd924b6b096e 08f621827444f70d 884f5d0240d2712e 10e116e9192af3c9 1a7ec57647e39340 57340b4cf408d5a5 6592f8274eec53f0
and for "" it is:
SHA-3-224 6b4e03423667dbb7 3b6e15454f0eb1ab d4597f9a1b078e3f 5b5a6bc7 SHA-3-256 a7ffc6f8bf1ed766 51c14756a061d662 f580ff4de43b49fa 82d80a4b80f8434a SHA-3-384 0c63a75b845e4f7d 01107d852e4c2485 c51a50aaaa94fc61 995e71bbee983a2a c3713831264adb47 fb6bd1e058d5f004 SHA-3-512 a69f73cca23a9ac5 c8b567dc185a756e 97c982164fe25859 e0d1dcc1475c80a6 15b2123af1f5f94c 11e3e9402c3ac558 f500199d95b6d3e3 01758586281dcd26
Code
The following is an outline of the code:
import sys
from hashlib import sha3_224, sha3_256, sha3_384, sha3_512, shake_128, shake_256
data="abc"
if (len(sys.argv)>1):
data=sys.argv[1]
s = sha3_224()
s.update(data.encode())
print('SHA-3 224 bit: ',s.hexdigest())
s = sha3_256()
s.update(data.encode())
print('SHA-3 256 bit: ',s.hexdigest())
s = sha3_384()
s.update(data.encode())
print('SHA-3 384 bit: ',s.hexdigest())
s = sha3_512()
s.update(data.encode())
print('SHA-3 512 bit: ',s.hexdigest())
print('\nKeccak\n')
print('\nShake\n')
s = shake_128()
s.update(data.encode())
print('Shake 128 bit: ',s.hexdigest(128//4))
s = shake_256()
s.update(data.encode())
print('Shake 256 bit: ',s.hexdigest(256//4))
SHA-3 was known as Keccak and is a hash function designed by Guido Bertoni, Joan Daemen, Michaël Peeters, and Gilles Van Assche. MD5 and SHA-0 have been shown to be susceptible to attacks, along with theoretical attacks on SHA-1. NIST thus defined there was a need for a new hashing method which did not use the existing methods for hashing, and setup a competition for competing algorithms.
In October 2012, Keccak won the NIST hash function competition, and is proposed as the SHA-3 standard. It should be noted that it is not replacement SHA-2, which is currently a secure methods. Overall Keccak uses the sponge construction where the message blocks are XORed into the initial bits of the state, and then invertibly permuted.
The sponge function takes a simple function f and involves a number of stages, and where we create a fixed output (dependent on the bit length of the hash function). Simple operations of XOR, AND, and bit shifts are used, and which leads to a fast generation of the hash function:
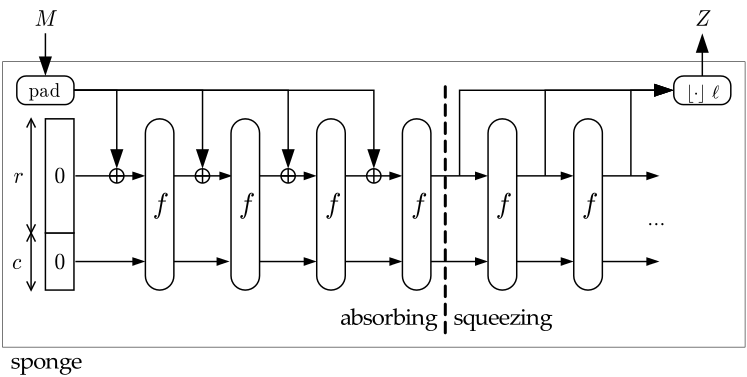
The f permutation function takes a variable-length input and produces an arbitrary output length. A value r is the bit rate, and each f function operates on b bits, and where a capacity is defined as c = b - r.
National Institute of Standards and Technology (NIST) has now released the final version of the method as a new standard: Federal Information Processing Standard (FIPS) 202, SHA-3 Standard: Permutation-Based Hash and Extendable-Output Functions.
NIST published the new standard on 5 August 2015 [here] and which beat off competition from BLAKE (Aumasson et al.), Grøstl (Knudsen et al), JH (Hongjun Wu), and Skein (Schneier et al.).
The SHAKE method is useful as it can be used to create a hash method of a variable length. For example the 128-bit version will produce a hash value is 32 hex characters.
The following is a presentation on SHA-3, SHAKE and Keccak [slides]:
 [
[