Hazmat HMAC with MD5/SHA-1/SHA-256/Blake2b/SM3HMAC (hash-based message authentication code) supports the usage of a key to hash data. This key is kept secret between Bob and Alice, and can be used to authentication both the data and that the sender still knows the secret. Overall HMAC can be used with a range of different hashing methods, such as MD5, SHA-1, SHA-256 (SHA-2), Blake2b, SM3 and SHA-3. This page outlines the HMAC-MD5 methods using the Hazmat cryptography layer. ShangMi 3 (SM3) is a hashing method that is defined with a Chinese National Standard. |
Theory
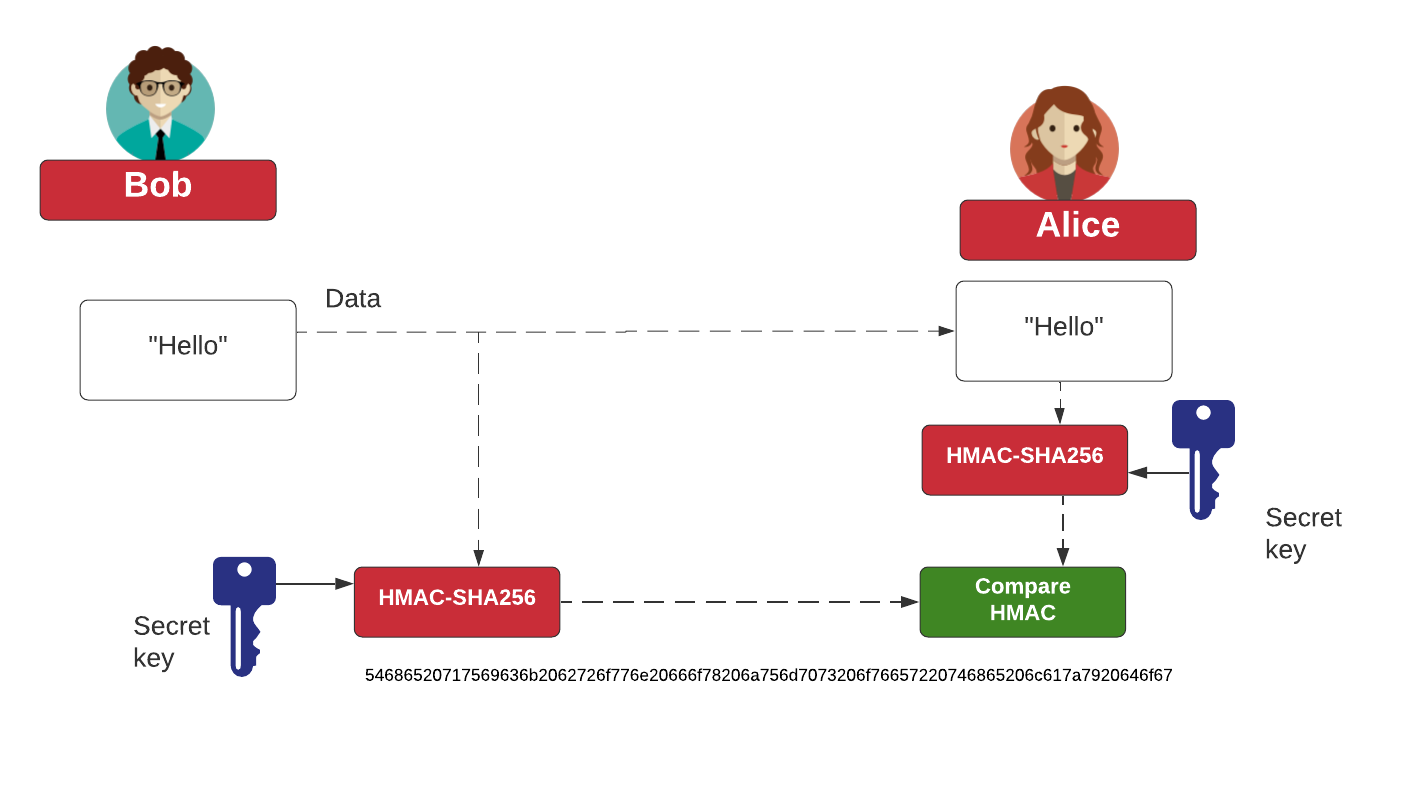
HMAC (hash-based message authentication code) supports the usage of a key to hash data. This key is kept secret between Bob and Alice, and can be used to authentication both the data and that the sender still knows the secret. Overall HMAC can be used with a range of different hashing methods, such as MD5, SHA-1, SHA-256 (SHA-2) and SHA-3:
One of the most useful library for crypto primitives in Python is called cryptography. It contain both "secure" primitives and a "hazmat" layer. Overall the "hazmat" layer should be treated with care, as it could contain security vulnerabilities. In this case we will implement a number of HMAC primitives with the "hazmat" layer.
from cryptography.hazmat.primitives import hashes, hmac
import binascii
import sys
st = "Hello"
k="qwerty123"
hash="MD5"
def show_hash(name,type,data,key):
digest = hmac.HMAC(key, type)
digest.update(data)
res=digest.finalize()
hex=binascii.b2a_hex(res).decode()
b64=binascii.b2a_base64(res).decode()
print (f"HMAC-{name}: {hex} {b64}")
if (len(sys.argv)>1):
st=str(sys.argv[1])
if (len(sys.argv)>2):
showhex=str(sys.argv[2])
if (len(sys.argv)>3):
k=str(sys.argv[3])
if (len(sys.argv)>4):
hash=str(sys.argv[4])
try:
data=st.encode()
key=k.encode()
print ("Data: ",st)
print (" Hex: ",binascii.b2a_hex(data).decode())
print ("Key: ",k)
print (" Hex: ",binascii.b2a_hex(key).decode())
print()
if (hash=="MD5"): show_hash("MD5",hashes.MD5(),data,key)
elif (hash=="SHA1"): show_hash("SHA-1",hashes.SHA1(),data,key)
elif (hash=="SHA224"): show_hash("SHA-224",hashes.SHA224(),data,key)
elif (hash=="SHA256"): show_hash("SHA-256",hashes.SHA256(),data,key)
elif (hash=="SHA512"): show_hash("SHA-512",hashes.SHA512(),data,key)
elif (hash=="SM3"): show_hash("SM3",hashes.SM3(),data,key)
elif (hash=="SHA3224"): show_hash("SHA3-256",hashes.SHA3_224(),data,key)
elif (hash=="SHA3256"): show_hash("SHA3-256",hashes.SHA3_256(),data,key)
elif (hash=="SHA3384"): show_hash("SHA3-384",hashes.SHA3_384(),data,key)
elif (hash=="SHA3512"): show_hash("SHA3-512",hashes.SHA3_512(),data,key)
elif (hash=="SHAKE128"): show_hash("SHAKE128 (32 bytes)",hashes.SHAKE128(32),data,key)
elif (hash=="SHAKE256"): show_hash("SHAKE256 (32 bytes)",hashes.SHAKE256(32),data,key)
elif (hash=="BLAKE2b"): show_hash("BLAKE2b (32 bytes)",hashes.BLAKE2b(32),data,key)
elif (hash=="BLAKE2s"): show_hash("BLAKE2s (32 bytes)",hashes.BLAKE2s(32),data,key)
except Exception as e:
print(e)
A sample run:
Data: Hello Hex: 48656c6c6f Key: qwerty123 Hex: 717765727479313233 HMAC-MD5: c3a2fa8f20dee654a32c30e666cec48e w6L6jyDe5lSjLDDmZs7Ejg==
 [
[