SipHash was published by Jean-Philippe Aumasson and Daniel J. Bernstein in 2012 [1], and addressed some of the issues caused by DoS attacks against hashing methods. It is a key-based hashing function, and where we can use a secret key to produce a hashed valued which cannot be reversed. This is useful in created a PRF (PseudoRandom Function). The hash is thus generated from a key (\(K_{in}\)) to give SipHash(\(D_{in}\),\(K_{in}\)). Without the knowledge of the key, it will be extremely difficult to determine the input data value. SipHash is seen as one of the best non-cryptography hashes around and is generally free from security issues. It uses a tree hash approach, and where we start by breaking up the input data and then hashing these together in a tree structure to eventually provide a root hash value. SipHash uses Intel's SIMD (Single Instruction, Multiple Data) extensions, and uses the 16 SIMD registers to perform fast multiplications. With SipHash we can apply a secret key to extend the range of hashes that are possible for a given input. In the following we will use a random key of 16 bytes (128 bits). Overall, for MACs, SipHash is more efficient than HMAC. We will also use BLAKE2b to create a MAC, and which uses a larger key.
Sodium: NaCl - Key-based Hashing (SipHash and BLAKE2b) |
Outline
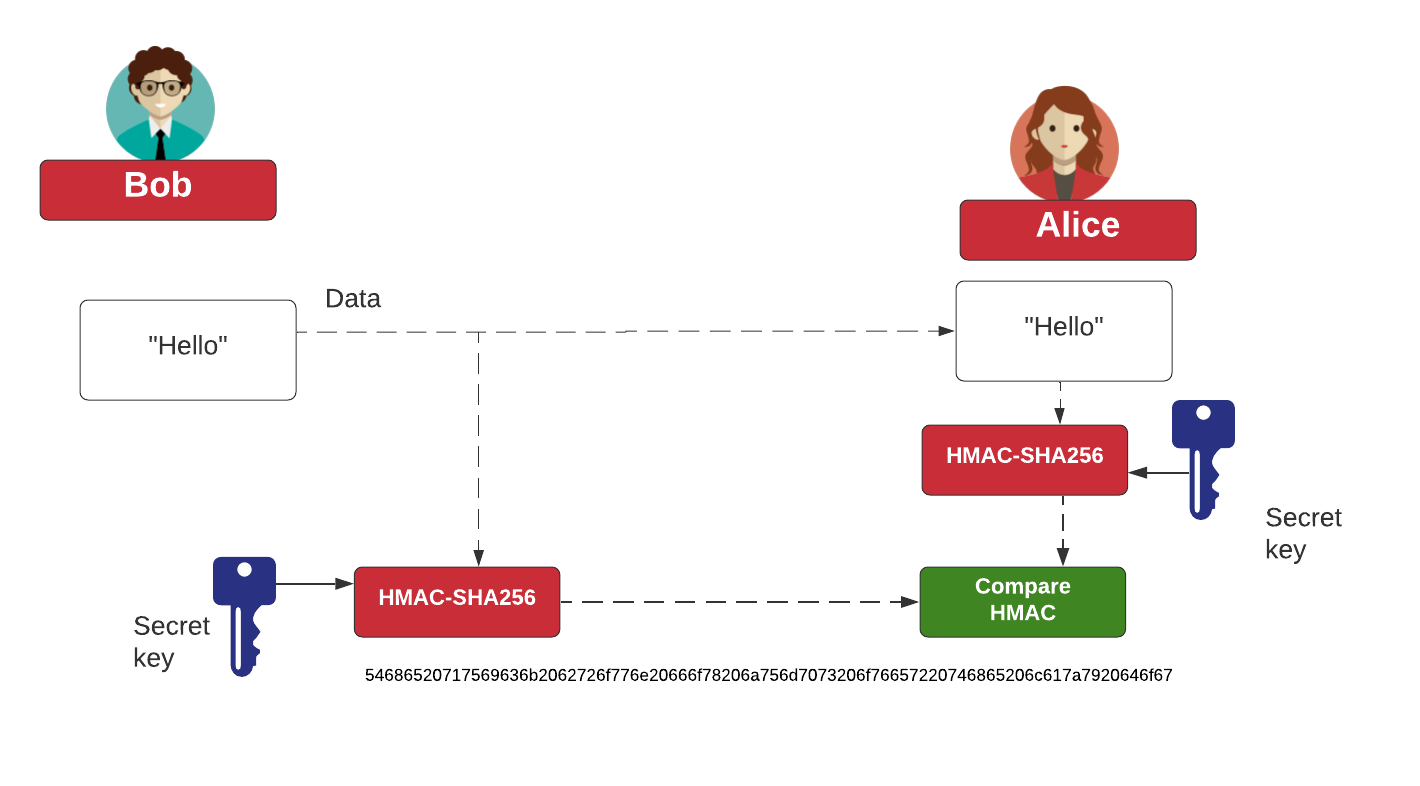
With SIPHash, we have a 128-bit key to produce an output hash, and can be used as a Message Authentication Code (MAC). With SIP, an intruder may have seen \(X\) and SipHash(\(X\), \(Key\)), but they cannot determine SipHash(Y, \(Key\)), if they do not know \(Key\) It produces a 128-bit output for SIP24, and 256-bit for SIPX24. An example of the MAC process is:
Coding
The coding is:
import nacl.encoding
import nacl.utils
from nacl.hash import blake2b,siphash24,siphashx24
import sys
message = 'Test 123'
if (len(sys.argv)>1):
message=str(sys.argv[1])
msg=message.encode()
auth_key = nacl.utils.random(size=32)
mac0 = blake2b(msg, key=auth_key, encoder=nacl.encoding.HexEncoder)
mac1 = siphash24(msg, key=auth_key[:16], encoder=nacl.encoding.HexEncoder)
mac2 = siphashx24(msg, key=auth_key[:16], encoder=nacl.encoding.HexEncoder)
print(f'Message is:\t{message}\n')
print(f'Shared key (BLAKE2b):\t{auth_key.hex()}')
print(f'Shared key (SIP):\t{auth_key.hex()[:16]}')
print('MAC (Blake2b):\t\t',mac0.decode())
print('MAC (SIPHASH-24):\t',mac1.decode())
print('MAC (SIPHASH-x24):\t',mac2.decode())
 [
[