CTR ModeI've previous outlined the problems with Electronic Code Book (ECB) here, especially that the same plain text results in the same cipher text, and how this can be overcome with Cipher Block Chaining (CBC) [here]. I've also outlined how you can recover from errors in the cipher by using a synchronised cipher stream, such as OFB (Figure 1) and described [here]. 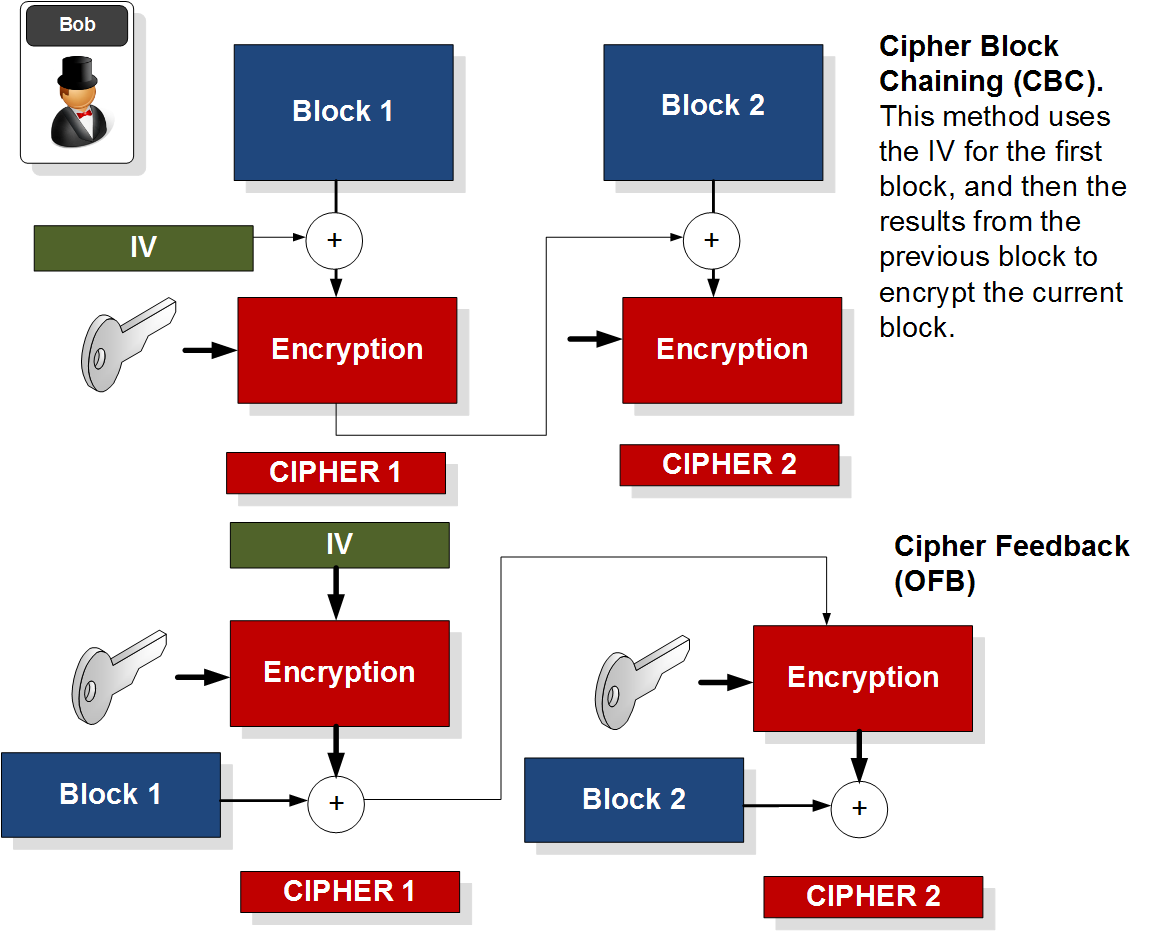
Figure 1 CTR ModeThe problem we now have is that the encryption and decryption processes will be slow as each stage depends on the previous stage, and we thus cannot apply parallel processing. An improved method is to use Counter (CTR) mode. As with OFB, Counter (CTR) mode converts the block cipher into a stream cipher. With this it generates a counter value and a nonce, and encrypts this, in order to EX-OR with the plain text block. The counter can increment by one each time, or can use a given algorithm (known only be the sender and trusted receiver). The advantage of this method is that the processing of each block is independent of the others, so we can apply parallel processing to each. In the previous methods discussed, we require the feedback from the other stages to feed into the current one, so we cannot apply parallel processing. 
Figure 2 nonce is a random number and is only used once. It is typically generated by one party and sent using a secure handshaking process. Often the nonce too is used for the generation of an IV, so that the counter doesn’t always start on the same value (or start at zero). CTR mode creates a cipher stream, where we can recover from errors, and where each bit can be processed one at a time. The other methods, such as CBC and OFB suffer from having to feed the output of one stage into another one. CTR mode overcomes this by supporting a counter for each block, and they thus can be processed independently of each other, at both the sending end and on the receiver. As OFB and CTR are both cipher streams they do not need to worry if the data fills blocks, and thus no padding is required. ECB and CBC both suffer from padding and where an intruder can examine the padding added in order to decipher the stream. With CTR, as with OFB, the transmitter and receiver work in the same way, and both encrypt the nonce and counter (so that there is no decryption processing involved). |