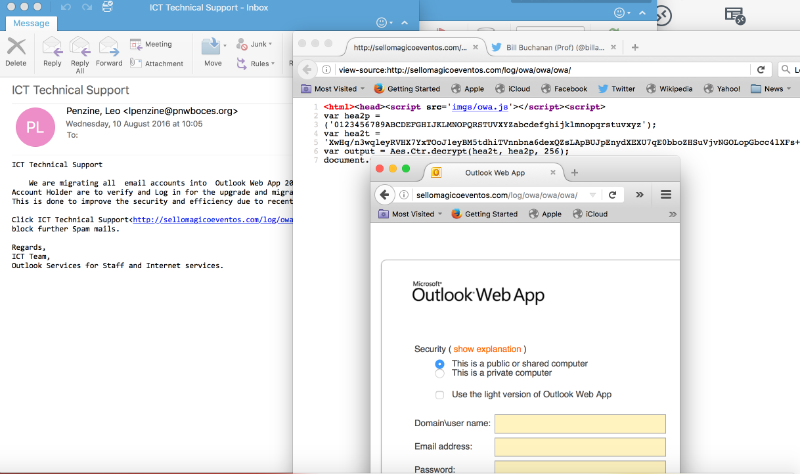
Obfuscating Malware (Part 3) - CryptoSpear phishing is still one of the most common forms on intrusion on a network. If one person in your corporate network clicks on a spear phishing email and either infects the computer with a backdoor, or enters their username and password, the intruder has found a way into the system. Often it is a low-level account that they are after, as these tend to not be detected, and allows the intruder to "case the joint". One way that an intuder can get past the email scanner is to encrypt the contents on the email. The following shows an encrypted email using JavaScript: [Part 1][Part 2]
The following shows the HTML in the email:
<html><head><script src='imgs/owa.js'></script><script>
var hea2p =
('0123456789ABCDEFGHIJKLMNOPQRSTUVXYZabcdefghijklmnopqrstuvxyz');
var hea2t =
'XwHq/n3w [...] yFz/19lQ==';
var output = Aes.Ctr.decrypt(hea2t, hea2p, 256);
document.write(output)</script></head></<html>
You can see that it has a Base64 message, which contains the AES crypto (hea2t) and the key (hea2p). This uses a 256-bit key, and the encrypted message is in hea2t and the password, from which the 256-bit key is generated from, is "012345678....xyz". This does enought to trick the email filtering system. The owa.js file contains the crypto Javascript. The library was not written for malicious purposes, but has been integrated by the spammer: 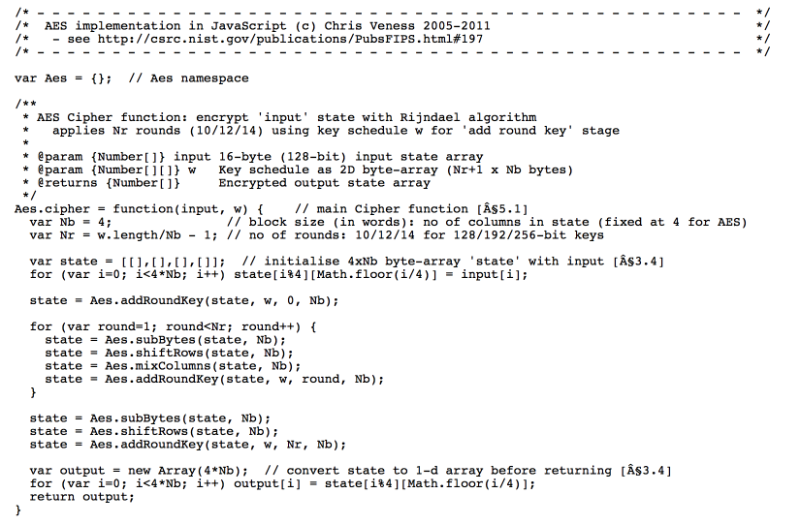
Other examplesHere are some other phishing examples: and: |