In the elliptic cryptography field we use a finite field and use a form of: \(y^2 = x^3 + a.x + b \pmod p\). The Mordell curve does not constrain the computation into a finite field and has the form of: \(y^2 = x^3 + n\). It was analysed by Louis Mordell and who showed that there are only a finite number of integer solutions to this. In this case, we will determine the integer solutions to a Mordell curve. The values of \(x\) which do not have an integer solution (up to 155) are: 6, 7, 11, 13, 14, 20, 21, 23, 29, 32, 34, 39, 42, 45, 46, 47, 51, 53, 58, 59, 60, 61, 62, 66, 67, 69, 70, 74, 75, 77, 78, 83, 84, 85, 86, 87, 88, 90, 93, 95, 96, 102, 103, 104, 109, 110, 111, 114, 115, 116, 118, 123, 124, 130, 133, 135, 137, 139, 140, 146, 147, 149, 153, and 155 [Finite Fields with the Mordell Curve].
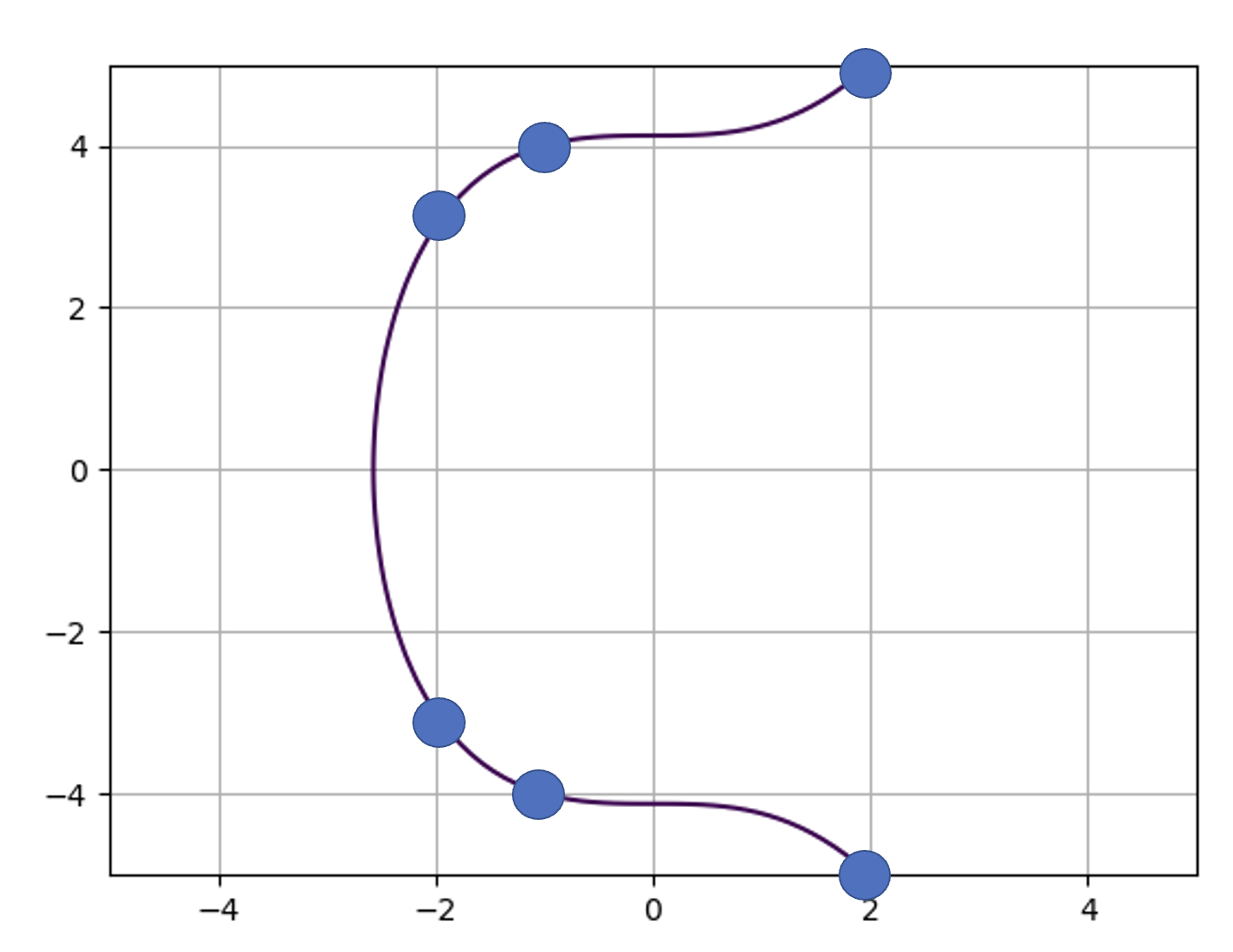
Mordell curveTheoryIn the elliptic cryptography field we use finite field and use a form of: \(y^2 = x^3 + a.x + b \pmod p\) The Mordell curve does not constrain the computation into a finite field and has the form of: \(y^2= x^3+ n\) The Mordell Curve comes from Louis Mordell and who showed that there are only a finite number of integer solutions to this. With \(y^2=x^3+17\), we 16 possible integer points [1]. If we plot the Mordell curve for \(y^2=x^3+17\), we get this [here]:
In this case, we can see that we have six possible points in the range of -2 to 2. In a finite field problem, we would normally be constrained with a prime number, and where we find the quadratic root. But, we are not constrained, so we will have to search manually. With this we will compute the solutions for values up to 100,000:
import math
import sys
r=100000
n=17
if (len(sys.argv)>1):
n=int(sys.argv[1])
print(f"y^2=x^3+{n}")
print ("Solutions: ")
for x in range(-20, r):
y_2 = x**3 + n
if (y_2>0):
y=math.sqrt(y_2)
if (y.is_integer()):
print ("Found: ",int (x),int(y))
A run of this shows:
Found: -2 3
Found: -1 4
Found: 2 5
Found: 4 9
Found: 8 23
Found: 43 282
Found: 52 375
Found: 5234 378661
And we can see we have eight points of (-2,3), (-1,4), (2,5), (4,9), (8,23), (43, 282), (52,375) and (5234,378661). Then we can add the negative values of y to get the rest of the points: (-2,-3), (-1,-4), (2,-5), (4,-9), (8,-23), (43, -282), (52,-375) and (5234,-378661). If we sample a few we get: For (-2,-3) → (-3)² = (-2)³ + 17 -> 9 = 9 For (43,282) -> (282)² = (43)³ + 17 -> 79524 = 79507 + 17 The known points are:
n (x,y)
1 (−1, 0), (0, 1), (2, 3)
2 (−1, 1)
3 (1, 2)
4 (0, 2)
5 (−1, 2)
6 –
7 –
8 (−2, 0), (1, 3), (2, 4), (46, 312)
9 (−2, 1), (0, 3), (3, 6), (6, 15), (40, 253)
10 (−1, 3)
11 –
12 (−2, 2), (13, 47)
13 –
14 –
15 (1, 4), (109, 1138)
16 (0, 4)
17 (−1, 4), (−2, 3), (2, 5), (4, 9), (8, 23), (43, 282), (52, 375), (5234, 378661)
18 (7, 19)
19 (5, 12)
20 –
21 –
22 (3, 7)
23 –
24 (−2, 4), (1, 5), (10, 32), (8158, 736844)
25 (0, 5)
ConclusionsOur online security is highly dependent on elliptic curve methods, so thank them for knowing that you have a secure encryption tunnel when connecting to Web sites. Under the hood, we use ECDH (Elliptic Curve Diffie Hellman) and which often uses the P256 curve. For Bitcoin, we use: \(y^2=x^3 + 7 \pmod p\) References[1] Brown, E., & Myers, B. T. (2002). Elliptic curves from Mordell to Diophantus and back. The American mathematical monthly, 109(7), 639–649. |
 [
[