Symmetric Key
With symmetric key, we use the same key to encrypt and to decrypt. The most popular symmetric key methods are AES and ChaCha20. In its pursest form, AES is a block cipher, with 128-bit block sizes. ChaCha20 is a stream cipher. With a block cipher we need padding, and there is no padding required for a stream cipher. The main modes that we get with symmetric key are ECB (Electronic Code Book), CBC (Cipher Block Chain), CTR (Counter) and GCM (Galois Counter Mode), and with either a 128-bit or a 256-bit encryption key. With symmetric key we can also use AEAD (Authenticated Encryption with Associated Data), and which allows additional data to be added into the cipher, and which can then be used to authenticate it. This additional data might relate to a session number.
|
Method
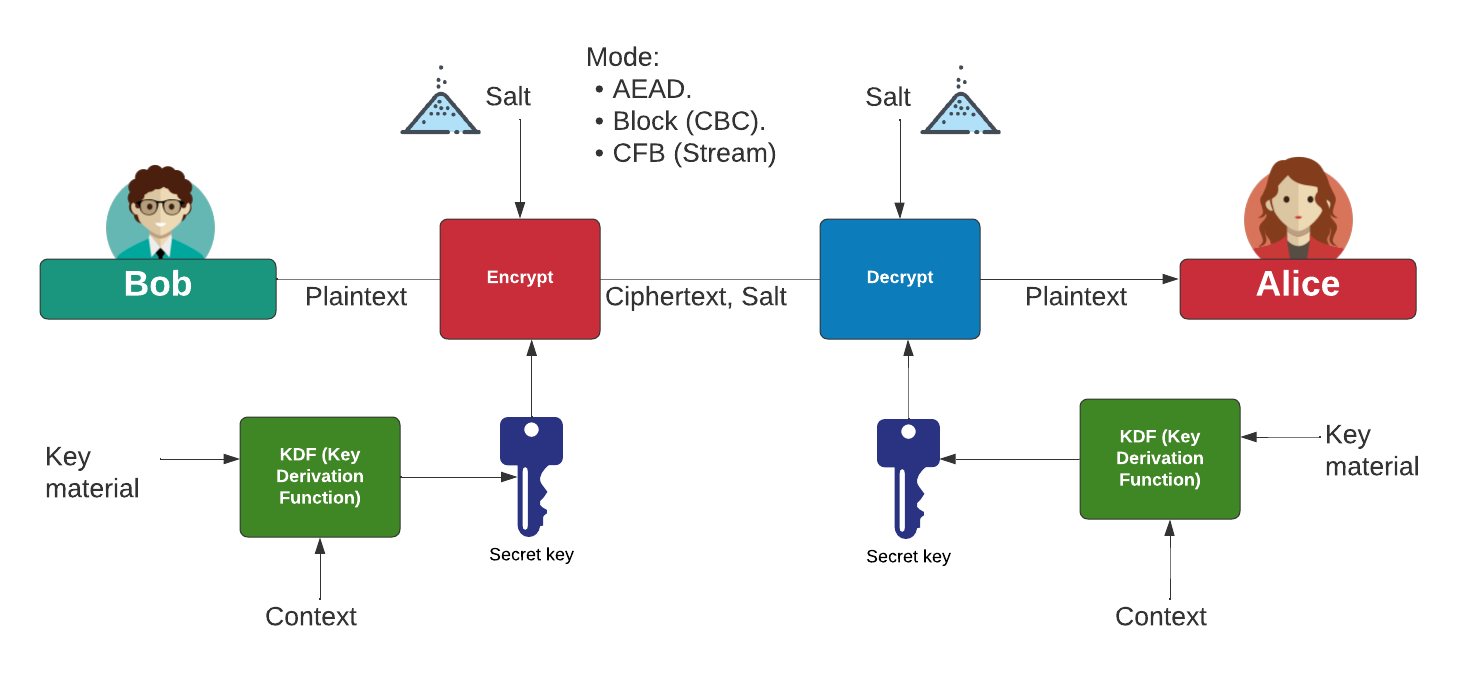
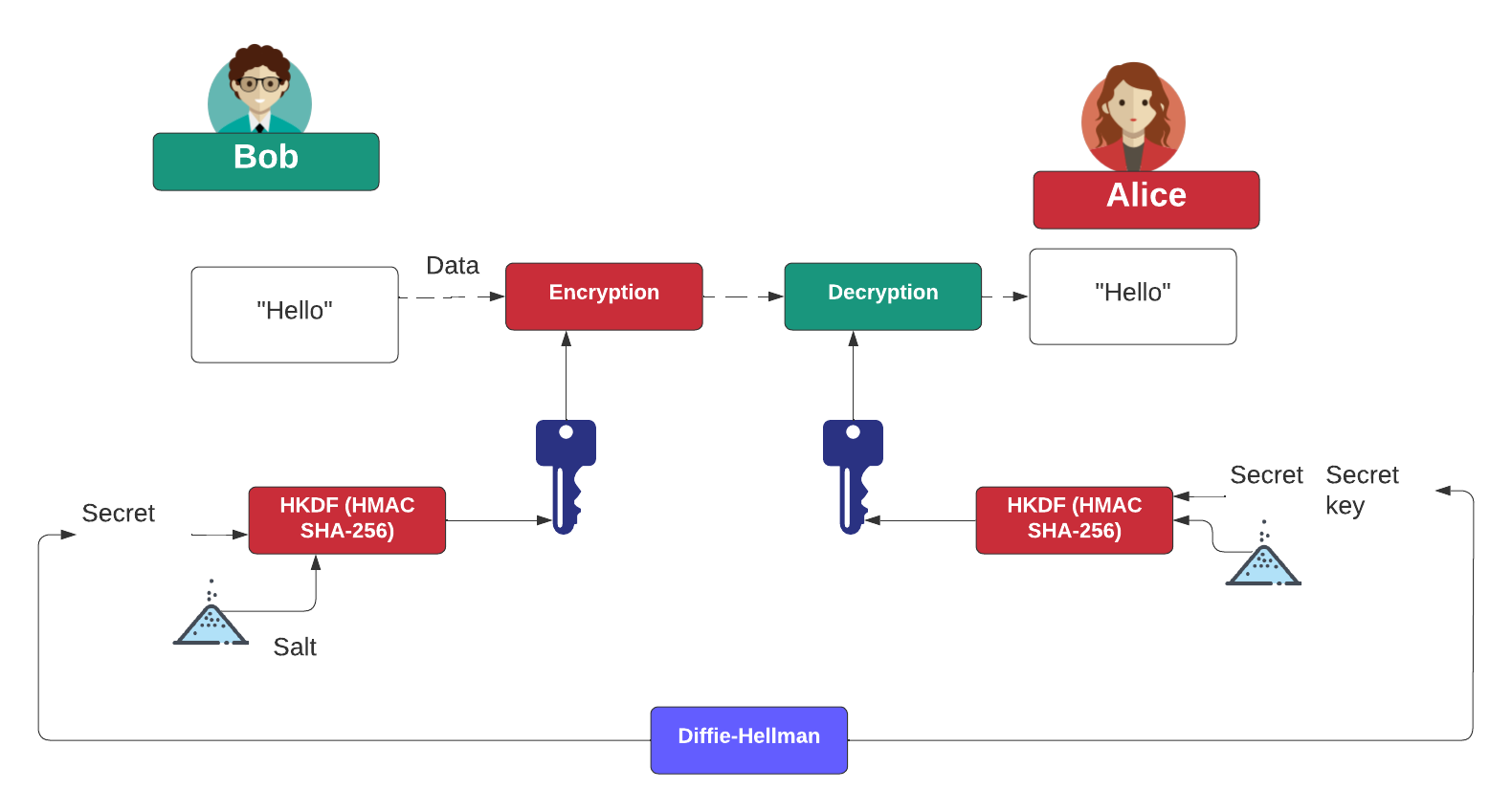
With symmetric key, Bob and Alice use the same encryption key to encrypt and decrypt:
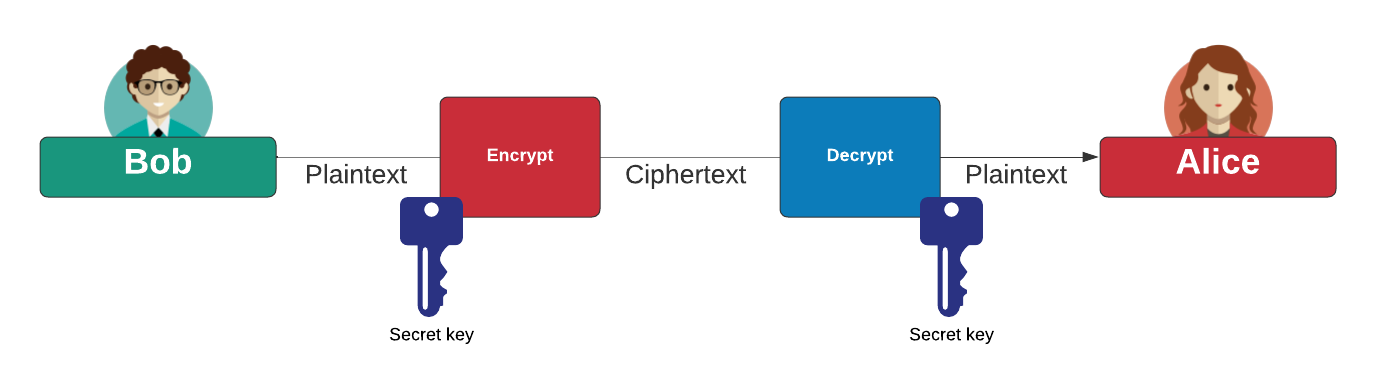
We can create a block cipher (such as with CBC mode), a stream cipher (such as ChaCha20) or AEAD (Authenticated Encryption with Additional Data). To generate the encryption key we can use a KDF (Key Derivation Function). For most modes, we add a salt (or nonce) values to the cipher process. This salt must be stored alongside the cipher, so that we can decrypt the cipher with the same salt and the same key. With AEAD, we add some additional data which is known by both sides, such as a session ID. A common cipher for AEAD is AES GCM and ChaCha20/Poly1305.
In order to pass the key from Bob to Alice, we can use the Diffie-Hellman key exchange method, and which will end up with the same shared secret:
Presentation

 [
[